-
Latest Version
-
Operating System
Windows XP64 / Vista64 / Windows 7 64 / Windows 8 64
-
User Rating
Click to vote -
Author / Product
-
Filename
Wireshark-win64-1.12.5.exe
-
MD5 Checksum
cd0e2251104e08fc84428c57d1fd787d
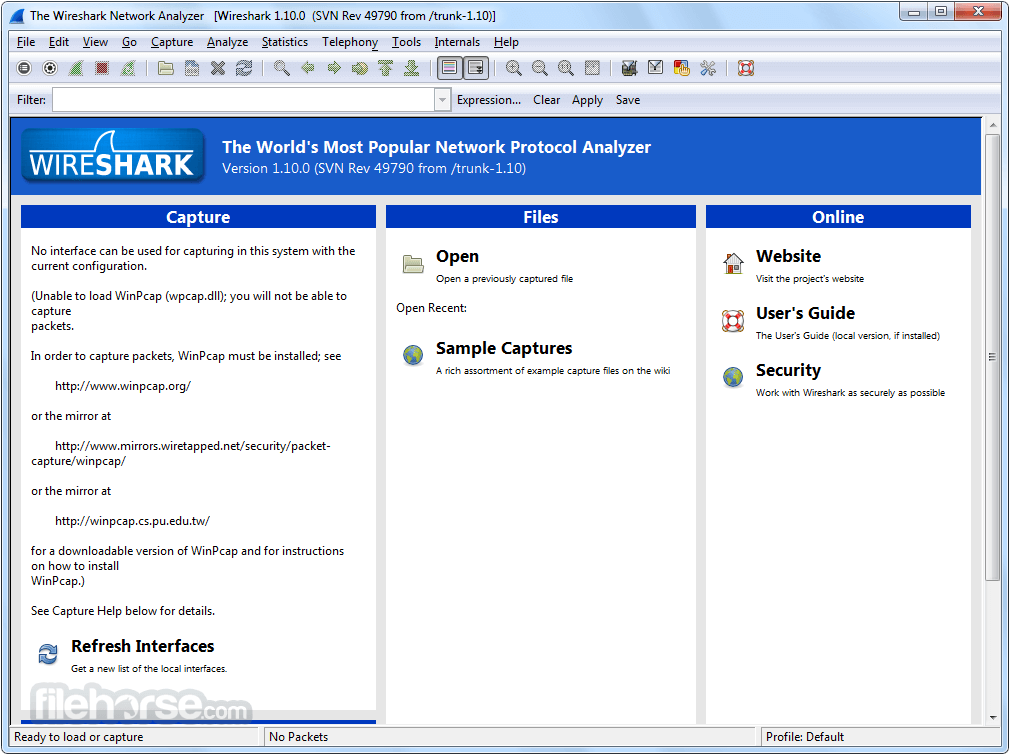
Sometimes latest versions of the software can cause issues when installed on older devices or devices running an older version of the operating system.
Software makers usually fix these issues but it can take them some time. What you can do in the meantime is to download and install an older version of Wireshark 1.12.5 (64-bit).
For those interested in downloading the most recent release of Wireshark (64-bit) or reading our review, simply click here.
All old versions distributed on our website are completely virus-free and available for download at no cost.
We would love to hear from you
If you have any questions or ideas that you want to share with us - head over to our Contact page and let us know. We value your feedback!
What's new in this version:
The following vulnerabilities have been fixed:
- The LBMR dissector could go into an infinite loop. (Bug 11036) CVE-2015-3808 CVE-2015-3809
- The WebSocket dissector could recurse excessively. (Bug 10989) CVE-2015-3810
- The WCP dissector could crash while decompressing data. (Bug 10978) CVE-2015-3811
- The X11 dissector could leak memory. (Bug 11088) CVE-2015-3812
- The packet reassembly code could leak memory. (Bug 11129) CVE-2015-3813
- The IEEE 802.11 dissector could go into an infinite loop. (Bug 11110) CVE-2015-3814
- The Android Logcat file parser could crash. Discovered by Hanno Böck. (Bug 11188) CVE-2015-3815
The following bugs have been fixed:
- Wireshark crashes if "Update list of packets in real time" is disabled and a display filter is applied while capturing. (Bug 6217)
- EAPOL 4-way handshake information wrong. (Bug 10557)
- RPC NULL calls incorrectly flagged as malformed. (Bug 10646)
- Wireshark relative ISN set incorrectly if raw ISN set to 0. (Bug 10713)
- Buffer overrun in encryption code. (Bug 10849)
- Crash when use Telephony / Voip calls. (Bug 10885)
- ICMP Parameter Problem message contains Length of original datagram is treated as the total IPv4 length. (Bug 10991)
- ICMP Redirect takes 4 bytes for IPv4 payload instead of 8. (Bug 10992)
- Missing field "tcp.pdu.size" in TCP stack. (Bug 11007)
- Sierra EM7345 marks MBIM packets as NCM. (Bug 11018)
- Possible infinite loop DoS in ForCES dissector. (Bug 11037)
- "Decode As…" crashes when a packet dialog is open. (Bug 11043)
- Interface Identifier incorrectly represented by Wireshark. (Bug 11053)
- "Follow UDP Stream" on mpeg packets crashes wireshark v.1.12.4 (works fine on v.1.10.13). (Bug 11055)
- Annoying popup when trying to capture on bonds. (Bug 11058)
- Request-response cross-reference in USB URB packets incorrect. (Bug 11072)
- Right clicking in Expert Infos to create a filter (duplicate IP) results in invalid filters. (Bug 11073)
- CanOpen dissector fails on frames with RTR and 0 length. (Bug 11083)
- Typo in secp521r1 curve wrongly identified as sect521r1. (Bug 11106)
- packet-zbee-zcl.h: IS_ANALOG_SUBTYPE doesn’t filter ENUM. (Bug 11120)
- Typo: "LTE Positioning Protocol" abbreviated as "LPP", not "LLP". (Bug 11141)
- Missing Makefile.nmake in ansi1/Kerberos directory. (Bug 11155)
- Can’t build tshark without the Qt packages installed unless --without-qt is specified. (Bug 11157)
Updated Protocol Support:
- AllJoyn, ASN.1 PER, ATM, CANopen, Diameter, ForCES, GSM RLC/MAC, GSMTAP, ICMP, IEC-60870-5-104, IEEE 802.11, IMF, IP, LBMC, LBMR, LDAP, LPP, MBIM, MEGACO, MP2T, PKCS-1, PPP IPv6CP, RPC, SPNEGO, SRVLOC, SSL, T.38, TCP, USB, WCP, WebSocket, X11, and ZigBee ZCL
 OperaOpera 125.0 Build 5729.49 (64-bit)
OperaOpera 125.0 Build 5729.49 (64-bit) MalwarebytesMalwarebytes Premium 5.4.5
MalwarebytesMalwarebytes Premium 5.4.5 PhotoshopAdobe Photoshop CC 2026 27.2 (64-bit)
PhotoshopAdobe Photoshop CC 2026 27.2 (64-bit) BlueStacksBlueStacks 10.42.153.1003
BlueStacksBlueStacks 10.42.153.1003 OKXOKX - Buy Bitcoin or Ethereum
OKXOKX - Buy Bitcoin or Ethereum Premiere ProAdobe Premiere Pro CC 2025 25.6.3
Premiere ProAdobe Premiere Pro CC 2025 25.6.3 PC RepairPC Repair Tool 2025
PC RepairPC Repair Tool 2025 Hero WarsHero Wars - Online Action Game
Hero WarsHero Wars - Online Action Game TradingViewTradingView - Trusted by 60 Million Traders
TradingViewTradingView - Trusted by 60 Million Traders WPS OfficeWPS Office Free 12.2.0.23155
WPS OfficeWPS Office Free 12.2.0.23155








Comments and User Reviews