-
Latest Version
Sandboxie Classic 5.70.12 (32-bit) LATEST
-
Review by
-
Operating System
Windows 7 / Windows 8 / Windows 10
-
User Rating
Click to vote -
Author / Product
-
Filename
Sandboxie-Classic-x86-v5.70.12.exe
It offers secure web browsing by running your Web browser under the protection of Sandboxie Classic means that all malicious software downloaded by the web browser is trapped in the sandbox and can be discarded trivially.
It has enhanced privacy where browsing history, cookies, and cached temporary files collected while Web browsing stay in the app and don't leak into Windows. It prevents wear-and-tear in Windows by installing software into an isolated sandbox.
Since the Open Sourcing sandboxie is being released in two flavors the classical build with a MFC based UI and as plus build that incorporates new features and an entirely new Q’t based UI. All newly added features target the plus branch but often can be utilized in the classical edition by manually editing the sandboxie.ini file.
Benefits of the Isolated Sandbox Classic:
Secure Web Browsing
Running your Web navigator under the protection of Sandboxie means that all malicious software downloaded by the browser is trapped in the tool and can be discarded trivially.
Enhanced Privacy
Browsing history, cookies, and cached temporary files collected while internet browsing stay in the program and don't leak into Windows.
Secure E-mail
Viruses and other malicious software that might be hiding in your email can't break out of the app and can't infect your real system.
Windows Stays Lean
Prevent wear-and-tear in Windows by installing software into an isolated sandbox.
How to Use
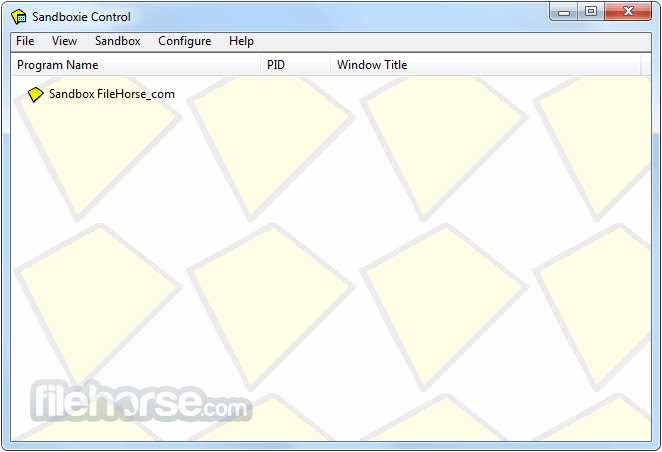
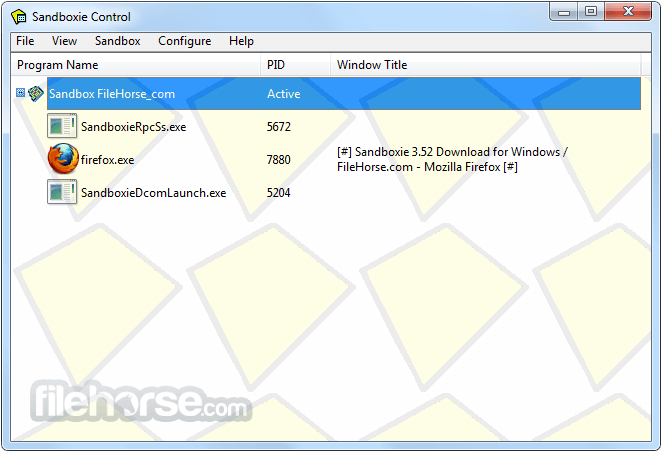
- Launch Sandboxie Control from the Start menu.
- Right-click on "DefaultBox" and select "Run Program".
- Choose a program to run in the sandboxed environment.
- Use the sandboxed application as usual.
- Close the application when done to remove changes.
- Empty the sandbox to delete all stored data.
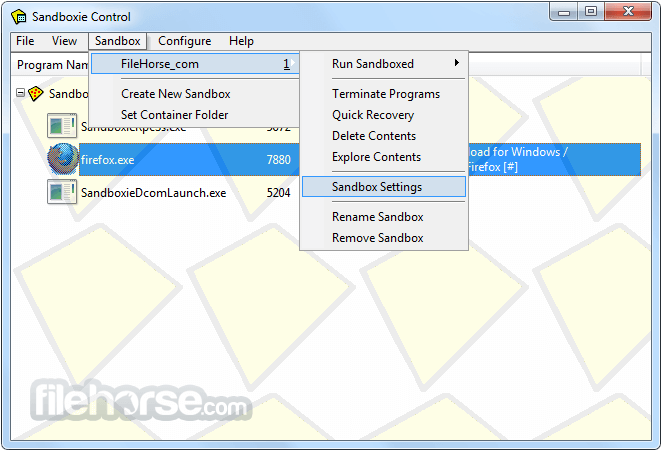
- Adjust settings in Sandboxie Control for customization.
- Run browsers in Sandboxie to prevent malware infections.
- Use separate sandboxes for different applications.
- Windows 7, 8, 10, or 11 (32-bit)
- 1 GHz processor or faster
- 1 GB RAM (2 GB recommended)
- 100 MB free disk space
- Internet connection for installation
- Enhances security against malware
- Prevents unwanted system changes
- Supports multiple sandboxes
- Lightweight and low resource usage
- Works with most Windows apps
- Limited functionality in free version
- Some apps may not work properly
- Requires manual sandbox cleanup
- Occasional compatibility issues
Also Available: Sandboxie (64-bit)
What's new in this version:
Added:
- added Indonesian translation to the Plus UI 4bad4d1
- added template for WeType Input Method (IME)
- added host name support to proxy configuration (looking up host at WSA_Startup)
- instead of binding to IP, Sandboxie can now bind to adapter (resolving IPs at WSA_Startup)
- added support for %ProgramFiles(x86)% variable
- added TemplateDefaultFolders containing all the default paths to be created in a privacy enhanced box
Changed:
- weird sort in the Move Sandbox list
- name and HwID information in the Support tab is now hidden by default but can be toggled as needed
- added alternative proxy relay implementation (instead of hacking existing sockets it starts relay threads) [EXPERIMENTAL]
Fixed:
- fixed the 'run in box' selection prompt not show BoxAlias
- fixed after Ctrl+F, the expansion and closure records of the Box Group were disrupted
- added additional checks to registry set/get functions 5a6a2f7
- fixed issue in Pool_Alloc 5a6a2f7
- fixed SbieCtrl.exe and SandMan.exe having a constant 3 MB/s IO rate in the Process Explorer
- fixed template for Tencent TIM causes drag and drop not available
- improved when Sandboxie.ini is huge, the response speed gets worse
- fixed MSI install can't create AppDataRoamingMicrosoft folder in Data Protection Box
- fixed two errors in Sandboxie about time speeding and add two time function hook
- fixed an issue where the translation string of the protocol selection was saved in the configuration file
- fixed box picker icon
- fixed when the UI language change, toolbar unchanged
- fixed PingInfoView gives an error when running in Sandboxie
- fixed CollectProducts() stuck in loop when Uninstall key not found
- fixed crashes with SbieDll.dll
- fixed OneDrive automatically downloads file when creating shortcut
 OperaOpera 125.0 Build 5729.49 (64-bit)
OperaOpera 125.0 Build 5729.49 (64-bit) MalwarebytesMalwarebytes Premium 5.4.5
MalwarebytesMalwarebytes Premium 5.4.5 PhotoshopAdobe Photoshop CC 2026 27.2 (64-bit)
PhotoshopAdobe Photoshop CC 2026 27.2 (64-bit) BlueStacksBlueStacks 10.42.153.1001
BlueStacksBlueStacks 10.42.153.1001 OKXOKX - Buy Bitcoin or Ethereum
OKXOKX - Buy Bitcoin or Ethereum Premiere ProAdobe Premiere Pro CC 2025 25.6.3
Premiere ProAdobe Premiere Pro CC 2025 25.6.3 PC RepairPC Repair Tool 2025
PC RepairPC Repair Tool 2025 Hero WarsHero Wars - Online Action Game
Hero WarsHero Wars - Online Action Game TradingViewTradingView - Trusted by 60 Million Traders
TradingViewTradingView - Trusted by 60 Million Traders WPS OfficeWPS Office Free 12.2.0.23155
WPS OfficeWPS Office Free 12.2.0.23155





Comments and User Reviews