-
Latest Version
Bitvise SSH Client 9.42 LATEST
-
Review by
-
Operating System
Windows 7 / Windows 8 / Windows 10 / Windows 11
-
User Rating
Click to vote -
Author / Product
-
Filename
BvSshClient-Inst.exe
Features and Highlights
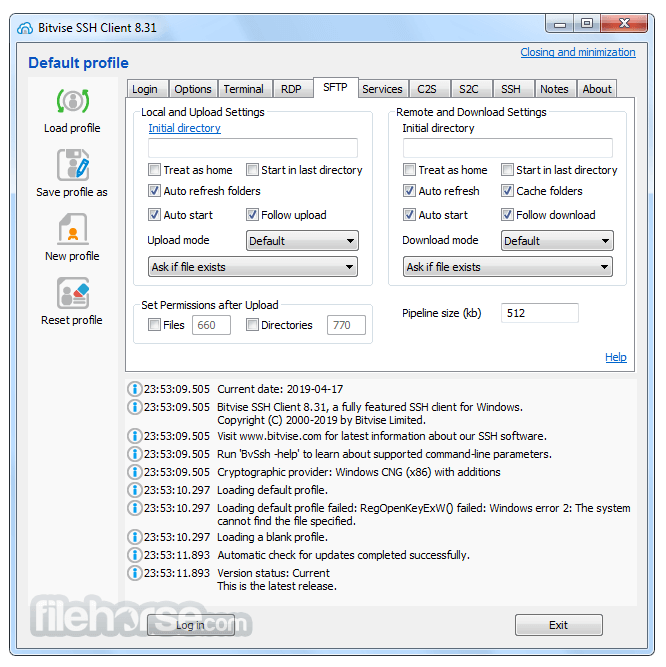
- One of the most advanced graphical SFTP clients.
- Single-click Remote Desktop forwarding.
- State-of-the-art terminal emulation with support for the bvterm, xterm, and vt100 protocols.
- Support for corporation-wide single sign-on using SSPI (GSSAPI) Kerberos 5 and NTLM user authentication, as well as Kerberos 5 host authentication.
- Support for ECDSA, RSA, and DSA public key authentication with comprehensive user keypair management.
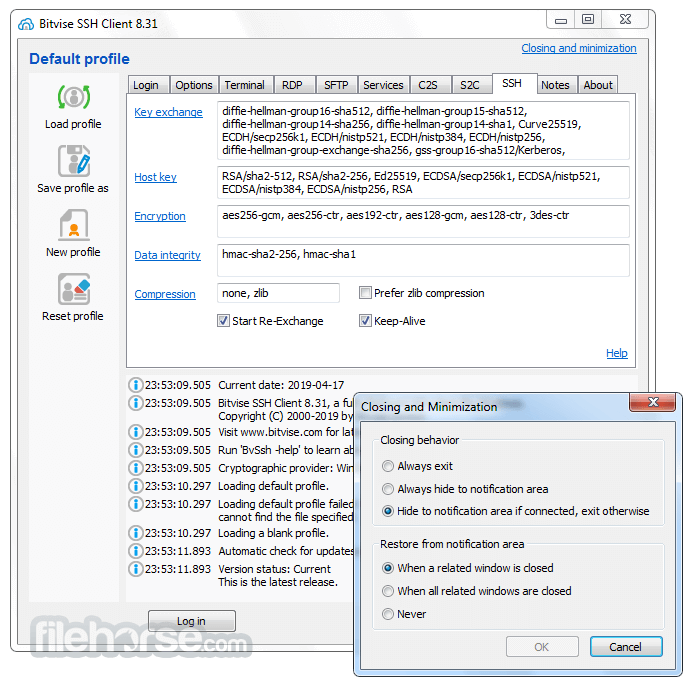
- Encryption and security: Provides state-of-the-art encryption and security measures suitable as part of a standards-compliant solution meeting the requirements of PCI, HIPAA, or FIPS 140-2 validation.
- Obfuscated SSH with an optional keyword. When supported and enabled in both the client and server, obfuscation makes it more difficult for an observer to detect that the protocol being used is SSH. (Protocol; OpenSSH patches)
- Powerful SSH port forwarding capabilities, including dynamic forwarding through integrated SOCKS and HTTP CONNECT proxy.
- Powerful command-line parameters which make the SSH client highly customizable and suitable for use in specific situations and controlled environments.
- An FTP-to-SFTP bridge allowing you to connect to an SFTP server using legacy FTP applications.
- An advanced, scriptable command-line SFTP client, sftpc.
- A scriptable command-line remote execution client, sexec, and a command-line terminal console client, stermc.
- A scriptable command-line tunneling client, stnlc, with support for static port forwarding rules, dynamic SOCKS-based tunneling, and FTP-to-SFTP bridge.
- .NET SSH library, FlowSshNet, with example PowerShell scripts showing how to use the SSH library for file transfer and remote program execution from PowerShell.
- Bitvise SSH Server remote administration features.
What's new in this version:
Bitvise SSH Client 9.42
FlowSshNet:
- In previous 9.xx versions, the FlowSshNet constructor Keypair.CreateFromData would block indefinitely if the application provided a passphrase-protected keypair, but the passphrase was incorrect. Fixed.
Bitvise SSH Client 9.41
Installation:
- Windows Server 2025 ships with Windows Terminal 1.18. This contains an issue where, if a console application enlarges the screen buffer height, Windows Terminal later crashes due to division by zero.
- In previous Bitvise software versions, the installer would enlarge the screen buffer height if it is small. If the installer is run with Windows Terminal as the console application, and Windows Terminal has not yet updated to a more recent version, this would cause a later installation step to fail with error code 0xC0000142. The issue does not occur if Windows Terminal has already updated.
- To improve compatibility with Windows Terminal, Bitvise installers no longer increase the screen buffer height if the console reports it as equal to the window height.
Command-line clients:
- The command-line clients sftpc, stermc, sexec and spksc no longer enable the no-flow-control extension by default, unless it is enabled using an explicit parameter. The extension prevents opening additional SSH channels, which prevents the use of the exec command in sftpc, and agent forwarding in stermc.
sftpc:
- sftpc now displays the default file transfer mode on startup. The default file transfer mode depends on the server and SFTP protocol version. It is either b (binary) or std (automatic text file detection; text files use SFTP v4+ text mode).
- sftpc now detects the Maverick SSHD server via the vendor-id extension, and sets the default file transfer mode for this server to binary instead of std. This SFTP server does not properly implement SFTP v4+ text mode, so the std file transfer mode causes file transfer errors.
SFTP:
- For downloads, text file auto-detection should now work with servers such as Maverick SSHD, which do not support re-reading data that was already read.
- When errors occur while using SFTP v4+ text mode, the error description will now include a remark that the file was opened using SFTP v4+ text mode.
- If the server sends a vendor-id SFTP extension, the information is now displayed or logged as part of the SFTP version message.
stermc:
- On Windows 10 versions up to 1909, the Windows function ScrollConsoleScreenBufferW can return errors even though it succeeds. stermc now ignores errors from this function on these Windows versions.
Bitvise SSH Client 9.39
General:
- When used with -noRegistry, the SSH Client would still create a disk-based lock file for update checking. The SSH Client now avoids creating this lock file when used with -noRegistry.
SSH:
- A server which identifies itself as SSH-2.0-HOSTED~FTP~ SFTP claims to support SSH_MSG_EXT_INFO, but disconnects if the client sends it. The SSH Client now automatically disables sending of SSH_MSG_EXT_INFO to this server by default. This is controlled by the setting Send EXT_INFO on the SSH tab in the main SSH Client window, or using the command-line parameter -sendExtInfo.
SFTP:
- The graphical SFTP interface now shows in its menus keyboard shortcuts which were already supported. Furthermore, the F3 shortcut for Edit was previously shown, but did not work. Fixed.
Terminal:
- If a server-side program enables mouse tracking in the terminal window, the graphical SSH Client's terminal now supports overriding mouse tracking (for selection and copy to clipboard) using either Shift key. Previously, only Left Shift would override mouse tracking.
Bitvise SSH Client 9.38
Graphical interface:
- The graphical SSH Client now supports command-line parameters for Window behavior preferences. Users who are running the SSH Client in a portable manner, or using the -noRegistry parameter; and who relied on the previous default for Closing behavior; can now select that behavior using the parameter: BvSsh -wndClose=hideIfConn
Bitvise SSH Client 9.35
sftpc:
- Improved behavior of the -noBuf parameter for put and get commands
Bitvise SSH Client 9.34
Installation:
- When installing using command-line parameters, the -autoUpdates parameter could previously be used only to disable automatic updates. It now also supports other values (stronglyRecommended, recommended or allAvailable).
- The FlowSshNet library, an optional SSH/SFTP scripting feature included with the SSH Client, now uses the Universal C Runtime. This allows the SSH Client to no longer include the outdated Visual C++ 2010 CRT. As a result, FlowSshNet is now installed only on Windows 7 SP1 or newer. (Previously, this feature was compatible with Windows Vista or newer.)
SFTP drive:
- Updated the WinFsp version included with the SSH Client to 2.0.23075.
- Improved the WinFsp installation process.
SSH:
- When connecting through an SSH jump proxy, interactive authentication methods can now be used to authenticate against the jump proxy. Previously, only pre-configured (unattended) authentication could be used.
- When the SSH Client fails to connect to a server, the error message now contains more detailed information about IP addresses to which the client attempted to connect.
stermc:
- In certain versions of Windows, the Windows function ScrollConsoleScreenBufferW fails if the destination coordinate is the same as the origin. This would cause previous stermc versions to exit with an error. Fixed.
sftpc:
- The sftpc command-line client now supports new get/put command parameters:
- -rv: Resume verifiably. Acts like -r for Resume, but does not resume unless the server supports synchronization using block-by-block hashing. This avoids corruption which is possible if heuristic resume detects the file can be resumed, but there are subtle changes in the middle of the file.
- -noSync: Disables synchronization using block-by-block hashing, even if the server supports it. This can be used with -r to achieve a faster heuristic resume, but corruption is possible if there are subtle changes in the middle of the file.
- -noBuf[=y|n]: If the server supports the extended SFTP attribute no-buffering@bitvise.com, this allows the user to express a preference whether the server should open the file for unbuffered I/O.
SFTP:
- The graphical SFTP interface now remembers its maximization state.
- The graphical SFTP interface now offers an option to clear recent folder history.
- When using cut & paste (rather than copy & paste) between Local and Remote panes, files are now moved instead of copied.
- In both graphical SFTP and sftpc, the Resume and Overwrite options are now once again available separately, even if the server supports synchronization using block-by-block hashing. This allows the user to express a preference to resume a file, but only if the partial destination file is unchanged relative to the source.
- When uploading, the SSH Client now includes the extended SFTP attribute intended-size@bitvise.com to communicate the final intended size of the file. This can help detect and diagnose incomplete transfers.
- The mirror feature would incorrectly remove destination files after they were mirrored, if the file names were present in the destination with a different case than in the source. Fixed.
- The mirror feature now supports a fast skip option which attempts to skip files which are present in both source and destination with the same size and last modification time. This can dramatically improve the speed of large mirror transfers where most files are unchanged, but at the cost of not verifying the content of skipped files.
Bitvise SSH Client 9.33
Security:
- Terrapin - CVE-2023-48795: Researchers have identified an issue where all SSH connections which use the encryption algorithm ChaCha20-Poly1305, or any integrity algorithm of type encrypt-then-MAC, are vulnerable to packet sequence manipulation by an active attacker, if the attacker can intercept the network path. This can be used to sabotage SSH extension negotiation. This affects extensions with security impact, such as server-sig-algs.
- Since the attacker can only remove packets sent before user authentication, this does not seem to fatally break the security of the SSH connection. However, it is a cryptographic weakness to address.
- Bitvise software versions 9.32 and newer support strict key exchange. This is a new SSH protocol feature which mitigates this attack. The SSH client and server must both implement strict key exchange for mitigation to be effective. Other SSH software authors are also releasing new versions to support this.
- If you must interoperate with SSH software which does not support strict key exchange, consider disabling the encryption algorithm ChaCha20-Poly1305, as well as integrity algorithms of type encrypt-then-MAC. These are the newer data integrity protection algorithms whose names contain -etm.
- Bitvise software versions 8.xx and older are not substantially affected because they do not implement algorithms where this issue is practically exploitable. Nevertheless, we suggest updating all SSH software to new versions that support strict key exchange.
- The encryption algorithms aes256-gcm and aes128-gcm are substantially immune from this attack. Users who are committed to older SSH software versions should consider using AES GCM. If this is not possible, the data integrity protection algorithms which are not named -etm are not entirely immune, but are also not believed to be practically exploitable. For compatibility with SSH software which does not support strict key exchange or AES GCM, an algorithm combination such as AES CTR with non-ETM data integrity protection may continue to be acceptable.
Graphical client:
- Error and warning popups would not be shown if the main SSH Client window was visible when the message was logged, but lost focus immediately after. This would happen, for example, if there was an issue with terminal session logging, which occurs just before opening the terminal window.
- The SSH Client now shows popups if the main window loses focus immediately after errors or warnings were logged
SFTP:
- The SSH Client now prefers to open remote files using the flags SSH_FXF_BLOCK_WRITE and SSH_FXF_BLOCK_ADVISORY, instead of only SSH_FXF_BLOCK_WRITE. This allows the server to strip the block flag if it is not supported by a part of its filesystem.
Bitvise SSH Client 9.31
Fixed:
Command-line clients:
- Even when output was redirected, the command-line clients sftpc, sexec, stermc, stnlc and spksc would not run unless the process was associated with a console window
User interface:
- Names and strings containing the & character were not properly displayed in lists
File transfer:
- When using the Move to dialog in the SFTP window, the SSH Client could crash
Bitvise SSH Client 9.28
Installation:
- If Install WinFsp was unchecked, the SSH Client installer would still unpack WinFsp files, without registering them. The installer will no longer unpack WinFsp files unless Install WinFsp is selected.
SSH:
- The SSH Client is now compatible with the OpenSSH-style authentication agent in 1Password. The SSH Client previously refused to connect to the Windows named pipe created by 1Password because the pipe owner is not a member of the Administrators group or Local System. For compatibility with this agent, the SSH Client no longer checks pipe ownership, but implements more validation of information received over the pipe.
Port forwarding:
- The command-line parameters -c2sFile and -s2cFile now also import comment fields, if present
Terminal:
- If the accent color was enabled for window title bars in Windows, the SSH Client's terminal window title could be hard to read
- Double-click word selection did not work correctly on the first word of the first line in the terminal window
- The terminal window now supports 5-hexadecimal-digit Unicode characters, i.e. Unicode code points higher than 65535
Bitvise SSH Client 9.27
Cryptography:
- OpenSSL version updated to 1.1.1t. Bitvise software primarily uses Windows CNG for cryptography. We use OpenSSL for specific cryptographic algorithms not supported by Windows. Currently, these are chacha20-poly1305 and on older Windows versions, the elliptic curve secp256k1. Our software does not use OpenSSL features affected by recent OpenSSL security advisories.
Terminal:
- The key combination Alt+Backspace would incorrectly open the terminal window's system menu. Fixed.
Bitvise SSH Client 9.26
EULA:
- We updated our EULAs to formalize our existing practices regarding the nature and behavior of our software (it is a product, not a service; the data it handles is not sent to Bitvise; risk tradeoffs with updates) and the way we provide support (via email and our case management system, in written form).
Installation:
- The SSH Client installer now offers the option whether to install WinFsp. WinFsp is required to use the SSH Client's SFTP drive feature, but is not needed for other functions.
- The SSH Client can now use WinFsp installed from another source, such as the official WinFsp distribution, or installed by a third-party application, instead of installing its own. We cannot guarantee reliability or performance when using such other versions of WinFsp. However, the SSH Client now tries to use them.
Cryptography:
- OpenSSL version updated to 1.1.1s. Bitvise software primarily uses Windows CNG for cryptography. We use OpenSSL for specific cryptographic algorithms not supported by Windows. Currently, these are chacha20-poly1305 and on older Windows versions, the elliptic curve secp256k1.
Terminal:
- Since version 9.23, the SSH Client's terminal window disables client-side scrolling when the server switches to the alternate screen. This is correct behavior, and it avoids confusing users, but it has confused other users, who were used to scrolling in the alternate screen.
- The SSH Client's terminal window now displays a padlock icon in the title bar when the alternate screen is enabled. This indicates that the terminal window is in a special state and explains why scrolling is disabled.
- The SSH Client's terminal window did not work on Windows XP. Fixed.
SSH Server Remote Control Panel:
- When using the SSH Client to remotely administer Bitvise SSH Server, the SSH Server Remote Control Panel would exit unexpectedly when trying to manually apply an update. Fixed.
Bitvise SSH Client 9.25
Graphical client:
- User Authentication Banner dialog text can now be selected and copied to clipboard
- Improved default file browse filter for client authentication keypair import
Bitvise SSH Client 9.24
General:
- SSH Client help windows now allow selection and copy & paste
- Updated keyboard shortcuts in the pop-up menu for the SSH Client icon in the system notification area. This resolves conflicts and makes the shortcut keys consistent with Ctrl+Shift shortcuts in SSH Client windows.
SSH:
- The SSH Client now displays the signature algorithm used during client authentication with a public key
- The default list of submethods for keyboard-interactive authentication is now empty
Command-line clients:
- Improved output of command-line clients when output is piped into another program, or redirected into a file
sftpc:
- When output is redirected, sftpc no longer truncates file and directory paths shorter than 1,000 bytes. For easier processing, file transfer results such as "OK" and "in sync" are now displayed as "" and ""
- The remove/delete commands del, ldel, rm, lrm, rmdir and lrmdir now support the -ifExist parameter. If passed, this parameter causes the command to test whether the path exists before attempting to delete it. If the path does not exist, the command succeeds.
Terminal:
- Due to Ctrl+Shift+... keyboard shortcuts new in versions 9.xx, the terminal window in the graphical SSH Client would no longer send to the server Ctrl+Shift key combinations such as Ctrl+Shift+F1. These combinations are now sent again.
- The clear command now causes the terminal window to scroll down instead of overwriting visible screen content
- A full reset, or a soft terminal reset, now avoids clearing the primary screen buffer, such as when the screen command exits
Bitvise SSH Client 9.23
Terminal:
- When the alternative window buffer is activated, the terminal window now prevents client-side scrolling. This interfered with display of server-side applications which provide their own scrolling via keyboard.
SFTP drive:
- There exist servers, such as GlobalSCAPE, which support neither the SFTP request space-available, nor the alternative statvfs@openssh.com. These requests are used to query free space on the server. With such servers, this information cannot be queried, so the SSH Client will now report a very large amount of free space on the SFTP drive. The client previously reported zero free space, which prevented some applications from writing files.
Bitvise SSH Client 9.19
Terminal:
- Restored behavior from previous SSH Client versions, including 8.xx, where right-click can be used immediately after selecting to copy-and-paste the selected text
- The DECSTBM message (Set Top and Bottom Margins) should now be handled correctly
spksc:
- The command-line client for the SSH Public Key Subsystem, spksc, now supports commands to list local keys in addition to public keys configured for public key authentication on the server.
- If Ctrl+C was pressed during command execution, spksc would previously hang
Host key manager:
- When using the Modify Host Key dialog, pasting a host address containing spaces would cause the SSH Client to crash
Bitvise SSH Client 8.53
- When using one of the key exchange methods with Diffie Hellman group exchange, the SSH Client and FlowSsh could perform an invalid memory access. Invalid DH group size parameters could be sent to the server. Fixed.
Security Clarification:
- We are receiving many inquiries about whether our software is affected by the recent Log4j vulnerability CVE-2021-44228
- Bitvise software does not use Log4j, and does not interact with it
Bitvise SSH Client 8.52
This is not a new feature release, but a successor to 8.49 with continued maintenance updates:
Graphical client:
- Certain user interface elements would not display correctly on Windows 11. Fixed.
Command-line use:
- The SSH Client's command-line clients (sftpc, stermc, sexec, stnlc, spksc) now support the widely accepted "--" syntax to identify the end of named parameters and the beginning of positional parameters.
Bitvise SSH Client 8.49
SFTP:
- When used under Parallels for Mac, the SSH Client was unable to list folders shared by the Mac (for example, MacHomeDesktop). This arose because the SSH Client used an advanced Windows filesystem API which the Mac does not implement. The SSH Client now uses a simpler version of this API, allowing the listing of Mac folders.
sftpc:
- The get command now supports a -wait switch. This causes the get command to wait for the server's confirmation that the file has been closed before continuing any further actions. When used with conjunction with -del, this causes sftpc to wait for the server's confirmation that the file has been closed before attempting to delete the file.
- sftpc now supports a new wait command. This causes sftpc to wait until it receives from the server any pending confirmations for file and directory close requests, before proceeding with any other actions. If there are no outstanding close requests pending confirmations, the wait command does nothing.
stermc:
- When using the stermc terminal shell command-line client, if the remote shell exited with a non-zero exit code, the SSH Client's totermc or bvtermc terminal client process would continue to run after stermc exits. These processes would potentially interfere with console input. Fixed.
Command-line clients:
- When input or output is redirected, then by default, the SSH Client's command-line clients (including sftpc, sexec, stnlc, stermc and spksc) will now use the input/output code page associated with the console in which they run (Windows functions GetConsoleCP and GetConsoleOutputCP), instead of the system-wide ANSI code page (Windows function GetACP). This causes output from Bitvise command-line clients to respect the code page set using chcp. For example, when chcp has been used, sftpc >> file.txt will now use the same code page as echo xxxx >> file.txt.
- Improved BOM handling when output is redirected with code pages UTF-8, UTF-16, and UTF-16BE. The BOM will now be consistently emitted when redirecting into an empty file, but not when redirecting into a non-empty file or a stream.
Bitvise SSH Client 8.48
General:
- The Notes tab is now scrollable and may contain much more text
SFTP:
- SSH Client version 8.46 introduced an issue where text file uploads would not work when using the file transfer modes Auto Std or Text, which are available in SFTP protocol versions 4 and 6. Fixed.
- When downloading a file using the Auto Std file transfer mode, which is available in SFTP protocol versions 4 and 6, the SSH Client first opens the file in binary mode. If the client detects that the file is textual, it closes and reopens the file using the flag SSH_FXF_TEXT_MODE.
- Some servers do not handle this scenario gracefully and do not allow the file to be reopened. With these servers, the Auto Std mode cannot work. In this case, the SSH Client will now display a more useful error to suggest changing the file transfer mode.
- The SFTP v4 draft specification from 2002 contains a typo in the definition of SSH_FILEXFER_ATTR_PERMISSIONS. This flag is defined with incorrect value 0x40 instead of the correct value, 0x04. This conflicts with previous and subsequent SFTP versions, as well as SSH_FILEXFER_ATTR_ACL defined in the same draft. Implementations should use the correct value, 0x04.
- There exist implementations of SFTP v4 that do not identify this error, and do not use the correct value. To aid compatibility with such servers, the SSH Client will no longer request SSH_FILEXFER_ATTR_PERMISSIONS as part of SSH_FXP_LSTAT if the Permissions column is not enabled on the Remote pane of the Browse tab.
Bitvise SSH Client 8.47
SSH:
- The SSH Client will now recognize a server with "MFT" in its SSH version string as a variant of "J2SSH_Maverick". This means the SSH Client will no longer send SSH_MSG_EXT_INFO by default to such servers. See the previous compatibility change for J2SSH_Maverick, in version history for SSH Client version 8.42.
Authentication:
- When the -keypairFile parameter is used to specify a password-protected keypair in a non-Bitvise format, and no valid passphrase is provided, the log message will now be more useful.
Remote Desktop:
- When using the single-click Remote Desktop forwarding feature on an ARM version of Windows, the SSH Client will now disable hooking of the Remote Desktop client (MSTSC). The SSH Client normally does this on Windows x86 and x64 so that the Remote Desktop window title can reflect the destination of the Remote Desktop connection. However, this prevented single-click Remote Desktop forwarding from functioning on ARM versions of Windows.
Bitvise SSH Client 8.46
SFTP:
- Since version 8.45, the SSH Client now uses SFTP v6 file open block flags SSH_FXF_BLOCK_WRITE and SSH_FXF_BLOCK_ADVISORY if the server advertises support for them. This helps avoid corruption of files while they are being transferred. We have received a report of a server that advertises support for these flags, but fails an open request if the flags are used. The SSH Client will now repeat an open request that fails this way, without the flags.
Command-line clients:
- When using Bitvise SSH Client command line clients sftpc, stermc, sexec, stnlc or spksc using a -keypairFile parameter that points to an encrypted keypair in non-Bitvise format, but without a -keypairPassphrase parameter that would provide a decryption passphrase, the SSH Client would display a cryptic error. The error is now less cryptic.
Bitvise SSH Client 8.45
Automatic updates:
- If the automatic update process encountered an error while downloading a new version installer from the primary download location, resulting in a partial executable being stored; and if download was then successful from the secondary download location; the resulting executable would be corrupted
- Improved the automatic update locking mechanisms
SSH:
- When displaying the host key received from the server, the SSH Client will now display the signature algorithm (e.g. RSA over SHA-256) rather than just the host key algorithm (e.g. RSA)
Graphical client:
- When the SSH Client was started hidden in the system notification area, it would cause a phantom Alt-Tab menu entry to appear
SFTP:
- When uploading files using SFTP v6; and if the server advertises support for either the block flag SSH_FXF_BLOCK_WRITE or the combination SSH_FXF_BLOCK_WRITE | SSH_FXF_BLOCK_ADVISORY; then the SSH Client will request one of these block flags when opening the file. This is to prevent premature actions by other server-side processes or file transfer clients that can modify or corrupt the file before the upload is complete.
- Uploading to a blind drop location that does not permit a directory listing could crash the SFTP window or the SSH Client process
- For improved compatibility with blind drops, it is now possible to navigate the Local and Remote panes to any location, even one that results in an error or does not allow a directory listing. An error dialog will be displayed when attempting to list such a directory, but it is now possible to try transferring files to or from such locations regardless.
Command-line clients:
- The log utility would output its own newlines as CRLF, but would record newlines from child processes as they were written by the process. If the child process used LF newlines (without CR), the output newline convention would be inconsistent. The log utility now consistently outputs newlines as CRLF.
Bitvise SSH Client 8.44
SSH:
- Bitvise SSH Client and FlowSsh will now recognize servers with "Maverick_SSHD" and "GoAnywhere" in their SSH version strings as variants of "J2SSH_Maverick". This means Bitvise SSH Client and FlowSsh will no longer send SSH_MSG_EXT_INFO by default to such servers. See the previous compatibility change for J2SSH_Maverick, in version history for Bitvise SSH Client and FlowSsh versions 8.42.
- If a client authentication key has been accepted by the server for authentication, the SSH Client will no longer prevent its use due to the server's server-sig-algs extension. In addition, the SSH Client will now log if a key is not used due to this extension.
- Graphical client:
- A new or reset profile will no longer open a terminal and SFTP window automatically, by default. This improves behavior when connecting to servers that limit SSH sessions to a single concurrent channel. Automatic opening of these windows can still be enabled using the same settings on the Options tab.
- The SSH Client's buttons would be hidden under Windows UI elements in Windows 10 Tablet mode. Fixed.
- The SSH Client will now display clearer information when an update is available but cannot be started.
Terminal:
- When using xterm and other non-bvterm protocols, the graphical SSH Client and stermc now support the sending of the following Alt + key combinations: Alt + Left Arrow, Right Arrow, Up Arrow, Down Arrow, Backspace, Page Up and Page Down. In addition, the graphical client also supports Alt + Enter. Alt + Enter is not supported in stermc because it is used by the Windows console to enter or exit full-screen mode
- When using xterm and other non-bvterm protocols, the speed of screen painting in the graphical SSH Client is now significantly improved
- The graphical SSH Client and stermc now support a terminal window resize initiated by an escape sequence from the server
- The graphical SSH Client and stermc will now accept xterm's 16-color and 256-color sequences even when regular xterm is in use (as opposed to xterm-16color or xterm-256color). This better supports programs such as byobu that send these sequences under plain xterm
- When switching between normal and alternate screens, the SSH Client would fail to clear the alternate screen. Fixed
- When using xterm and other protocols except bvterm and ANSI, the SSH Client would previously start set to use "application" cursor keys. To start with "standard" cursor keys, the setting Alt. cursor keys had to be enabled, or in stermc the parameter -altCurs had to be used
- The SSH Client will now start by default using "standard" cursor keys. The relevant setting has been replaced with App. cursor keys, and stermc now supports the parameter -appCurs to start instead with "application" cursor keys
- Changed Unicode character widths for about 6% of assigned Unicode code points from 0 to 1, and for another ~8% of code points from 2 to 1. This aligns more closely with character widths used by servers and avoids unintended discrepancies in rendering
- On the Terminal tab, the SSH Client's Default colors dialog now provides both the "Old Windows" and "New Windows" palette options. To match use of colors in other terminals, the New Windows palette is now the default choice. Previously, it was xterm
- The command line terminal client, stermc, now also supports the new palette choices using the -palette parameter
- When using bvterm, the new Windows 10 console produces cursor artifacts when the cursor is moved outside the viewport. The SSH Client now takes steps to avoid this
SSH Server Remote Control Panel:
- When using the CSV export feature in the SSH Server Remote Control Panel for SSH Server versions 8.xx, the CSV export would fail if the data contained a reversibly encrypted password or secret key
Bitvise SSH Client 8.43
Installation:
- The SSH Client adds its installation directory to the system PATH environment variable when installing, but did not remove it when uninstalling. The SSH Client installation directory is now removed from PATH when uninstalling. Reinstallations or upgrades from version 8.43 will briefly remove and then re-add the SSH Client installation directory to PATH.
SSH:
- Certain versions of the Pragma Fortress SSH server - including the most recent version when testing - can send a corrupted SSH authentication banner where an inexact, duplicate copy of the banner message is included before the language tag. SSH Client versions 7.xx and earlier could connect because they ignored the language tag, but SSH Client 8.xx versions would not because they check that the language tag does not exceed an unreasonable length.
- The SSH Client now allows an exception for this server where the incorrect encoding is ignored. If the server cannot be identified as "Pragma FortressSSH", the language tag length check remains enforced.
Command-line clients:
- Previously, an implied command such as the following:
sexec user@host dir /?
- ... would incorrectly cause command line clients including sftpc, stermc and sexec to display their own help text instead of invoking the remote command as specified. Fixed.
Graphical client:
- The graphical SSH Client now detects and warns about an insecure installation directory in an expanded, more thorough set of circumstances
- In version 8.42, the -sendExtInfo=... parameter was added to command line clients. An equivalent setting, Send EXT_INFO, is now also available in the graphical client, on the SSH tab
SFTP:
- Fixed an issue with auto-completion which could cause the SFTP graphical interface to dead-lock
Bitvise SSH Client 8.42
Installation:
- The SSH Client no longer supports installation on Windows 10 versions 1507 and 1511. These versions contain a flawed cryptographic implementation which prevents a number of SSH algorithms from working correctly. The lowest Windows 10 version supported is 1607.
- During an initial, interactive installation; when installing into a non-default directory (e.g. outside of C:Program Files (x86)); the SSH Client installer will attempt to detect if any parent of the installation directory grants insecure permissions for non-administrative users. The installer will display a warning about installing into such insecure directories.
- When updating an installation in such a directory, the update will succeed, but the graphical SSH Client will display a warning
Graphical client:
- Some versions of Nvidia Surround modify Windows behavior in a way such that the window manager doesn't respect the SSH Client's fixed window width setting. The graphical SSH Client now works around this issue.
- In the Host key manager interface, a host key could be incorrectly placed into the wrong recognized vs. unrecognized category if there were keys in both categories. Fixed.
Command-line clients:
- The command-line clients sftpc, sexec, stermc, stnlc and spksc now support the command-line parameter -sendExtInfo=n so that the user can disable sending of the client-side SSH_MSG_EXT_INFO message to a server which advertises support, but does not actually support it.
- Command-line clients will no longer display unnecessary warnings about failing to load update settings if the SSH Client was installed in an unattended manner and the graphical SSH Client has not yet been run.
SSH:
- In rare circumstances, an SSH session could terminate in such a way that the SSH Client would crash. Fixed
- The CrushFTP server, and other servers based on the J2SSH Maverick implementation, may advertise support for SSH_MSG_EXT_INFO (RFC 8308), but have a bug where the server disconnects if the client sends this message. Bitvise SSH Client and FlowSsh now attempt to detect these servers based on their SSH version strings, and disable sending of the client-side SSH_MSG_EXT_INFO if detected.
- OpenSSH 6.2 and 6.3 can be configured to enable AES GCM, but crash if it is used. Bitvise software versions 8.42 and higher will now disable AES GCM if the remote version string indicates an affected OpenSSH version.
SFTP:
- The SFTP server which identifies itself as "SSH-2.0-SFTP Server" has a flawed SFTP v4+ text mode implementation. The default transfer mode with this server will now be Binary instead of AutoStd.
The dialog interface for the Mirror feature could require multiple clicks on the OK button. Fixed.
Remote Desktop forwarding:
- The SSH Client now delays deletion of the Remote Desktop profile that mstsc is launched with. This is intended to improve compatibility with Windows on ARM64.
Terminal:
- The SSH Client's graphical terminal window implementation for classical terminals (xterm and other non-bvterm terminals) now implements improved mouse wheel scrolling, properly accumulating mouse wheel deltas.
- Some versions of Cmder have an issue which causes the Windows function ScrollConsoleScreenBuffer to fail unexpectedly. The bvterm client now works around this issue.
Bitvise SSH Client 8.38
- The SSH Client now supports machine-wide automatic update settings which can override user-specific settings. The SSH Client installer also supports command line parameters to configure automatic update settings.
- Changes in Bitvise SSH Server's terminal subsystem in versions 8.xx have made the bvterm protocol unreasonably slow with certain console applications. Bitvise SSH Server and SSH Client versions 8.38 implement optimizations in both the server and client to address these issues.
- sftpc: Pressing Esc on an empty line would incorrectly re-issue the last command. Fixed.
- When public key or private key import fails, a more accurate error message will now be displayed in certain cases
Bitvise SSH Client 8.37
- Fixed: when connecting through a proxy, if the setting Resolve DNS names locally was enabled, the SSH Client would often resolve DNS names remotely (via the proxy) anyway
Bitvise SSH Client 8.36
- Change log not available for this version
Bitvise SSH Client 8.35
- Fixed: with version 8.17, the profile settings RDP > Authentication > Password and Store encrypted password in profile were changed to take effect the same way as similar settings under Login > Authentication, but their UI layout was not updated
Bitvise SSH Client 8.34
- Change log not available for this version
Bitvise SSH Client 8.32
- Fixed an issue in how command line clients (sftpc, sexec, stermc, stnlc, spksc) were initializing the default key exchange algorithm list
Bitvise SSH Client 8.31
- This is not a new feature release, but a successor to 8.29 with continued maintenance updates. We skip versions containing zeros to avoid misunderstandings. For example, 8.03 and 8.30 might both be called "8.3"
- Added error descriptions for Windows error codes related to checking for new versions and downloading updates
- Fixed a memory safety issue which appears to be, but might not be, benign in most circumstances
Bitvise SSH Client 8.29
- Fixed an issue in previous 8.xx versions where, if the SSH Client had not been updated to a new version for longer than 42 days, trying to apply an update would fail due to a Windows registry Access denied error
Bitvise SSH Client 8.26
- Fixed issue introduced in version 8.25 where the recent locations drop-down in the graphical SFTP interface would no longer function correctly
- Fixed issue introduced in version 8.24 where the SSH Server Remote Control Panel could no longer be launched when connected to SSH Server versions 7.xx and earlier
Bitvise SSH Client 8.25
Graphical SFTP:
Auto-completion improvements:
- Regular files are no longer shown for auto completion of directory paths
- Tab and Shift+Tab now behave consistently with auto-completion in other apps
- File transfer events no longer cancel the auto-completion drop-down
- To improve UI responsiveness, directory listings are now performed in a background thread
Bitvise SSH Client 8.23
- Fixed an issue in previous 8.xx versions which would prevent Bitvise SSH Client and FlowSsh from connecting to a server that supports host key synchronization and employs a key type the client does not support. This affected connections from Windows XP and Windows Server 2003, where our cryptographic provider does not support Ed25519; and use under FIPS mode, where Ed25519 and ECDSA/secp256k1 are not supported
Bitvise SSH Client 8.22
- A proportion of users are closing the main SSH Client window when connected so that it minimizes into the Windows notification area (the system tray). Users forget about that SSH Client instance and launch new instances for new sessions. Forgotten sessions stay online indefinitely and terminal window settings do not appear to save because the SSH Client is never closed
- To fix this, the SSH Client will now restore its main window if it's still hidden in the notification area after closing a related window such as terminal or SFTP. This behavior can be configured with a new setting found under Closing and minimization
- Since the changes related to password authentication in 8.17, the graphical client's command line parameter -password=... did not take effect if the SSH Client profile was configured to use password authentication but the checkbox Store encrypted password in profile was disabled. Fixed
- sftpc: Updated help text for get and put commands to clarify how the -r and -o parameters control when hash-based synchronization, heuristic resume or overwrite is used
Bitvise SSH Client 8.21
- The graphical SSH Client's terminal window for xterm (and other non-bvterm terminals) implements a Select mode intended to behave like the Windows console's QuickEdit mode. A difference was catching users off-guard: canceling a mouse text selection with an arbitrary key press would not send the key to the server. For users who began a selection without noticing, it appeared as though the terminal window was eating a key press for no reason. Consistently with the Windows console, the SSH Client will now send key presses that cancel a selection to the server
- In previous versions, if the graphical SSH Client failed to load a profile specified on the command line, it would fall back to the last used profile and still act on the -loginOnStartup parameter if also provided. This would result in bewildering behavior. If a profile specified on the command line fails to load, the SSH Client now loads the default profile (stored in the Windows registry) and ignores -loginOnStartup
- In previous 8.xx versions, loading an SSH Client profile from a network share would fail when the ZoneId alternative data stream could not be opened. If the ZoneId ADS cannot be opened, a profile will now be loaded as if its origin is the local computer
- We have identified niche situations where one-click Remote Desktop forwarding might fail to start when an SSH Client DLL is not found. To resolve this, this version makes changes to how the Remote Desktop client is started
- There exist SSH clients which, in violation of RFC 4254, disconnect if a server sends a global request after successful authentication. A server might send a global request for purposes such as host key synchronization or disconnect detection. If the server supports RFC 8308, then to indicate it supports global requests, the SSH Client will include the extension global-requests-ok in its SSH_MSG_EXT_INFO
- In previous 8.xx versions, the SSH Client would not import RSA private and public keys larger than 8192 bits. This limit is once again 16384 bits
- The SSH Client installer will now offer to wait instead of exiting when another Bitvise installation is already in progress
- Slightly improved the user friendliness of the installer and uninstaller for command-line installations
Bitvise SSH Client 8.19
- In previous 8.xx versions, the icons for the New terminal console, New SFTP window and New Remote Desktop actions were too similar. The SSH Client now sports updated icons that are easier to distinguish
- In previous 8.xx versions, when the SSH Client reconnected after losing a connection, it failed to continue ongoing transfers. Fixed
- SFTP interface: When connecting to SFTP servers that support synchronization using the SFTP v6 extensions check-file-name, check-file-handle and check-file-blocks, the resume and overwrite modes are now more clearly overridden by synchronize in the SFTP user interface
- sftpc: When connecting to SFTP servers that support synchronization, the -r and -o options for get and put commands now both act as aliases for synchronize. Previously, only -o acted as an alias for synchronize, and -r was unavailable
Bitvise SSH Client 8.18
- In previous 8.xx versions, if the system clock was moved back after a check for updates (in UTC, not time zone specific), an automatic check would be repeated with high frequency. This could consume 80 kbps in bandwidth while the graphical SSH Client was running until the clock caught up. Fixed.
- In previous 8.xx versions, an automatic check for updates would be performed if the graphical SSH Client was run with -noRegistry. An automatic check is no longer performed in this situation, but can be performed manually
Bitvise SSH Client 8.17
- In version 8.15, loading a profile which was last saved by a previous version would cause the SSH Client to send an invalid elevation extension value to the server. This caused SSH Server versions 8.xx to disconnect. The SSH Client will now send a valid elevation extension value in this circumstance
- The Remote Desktop forwarding feature Use SSH login credentials would previously work only if the password authentication method was used for client authentication, but it did not work for password authentication over keyboard-interactive. This will now also work with password over keyboard-interactive
- In the graphical SSH Client, on the Login tab, setting Initial method to password could result in unintuitive behavior. Password change was not easily discoverable, and setting Initial method to password without entering a password caused the SSH Client to send an empty password at start of connection, incurring an authentication penalty
- This has been redesigned so that Initial method can be set to password without entering a password. In this case, a password dialog will dependably appear when connecting. As part of this change, it is no longer possible to enter a password on the Login tab without enabling Store encrypted password in profile
- In version 8.15, in command line clients, the -keypairFile parameter did not override a public key configured as an initial authentication method in a profile specified using -profile. The -keypairFile parameter will now once again override any public key configured in the profile
Bitvise SSH Client 8.15
Highlights:
- The SSH Client now supports automatic updates. An administrator can configure the SSH Client to automatically apply all updates; only recommended updates; only strongly recommended updates; to apply updates only manually; or to never check for updates
- Currently, the SSH Client does not install an update service. It needs to be started from time to time by an administrative user in order to apply updates
- The graphical SSH Client and sftpc now support recursive directory mirroring. A directory and all of its subdirectories and files can be synchronized either in the upload or download direction. The SSH Client can synchronize updated files and detect and automatically remove files and directories from the target location that are not present in the source
- The graphical SSH Client and sftpc can now display hashes (cryptographic digests) of local and remote files if the server supports the SFTP v6 check-file extension
- Bitvise SSH Client and SSH Server now implement automatic host key rotation. The SSH Client will synchronize keys from the SSH Server and any other servers that support the OpenSSH mechanism "hostkey update and rotation". The SSH Server will announce to clients all configured host keys, including those not employed, to facilitate host key rotation. The SSH Client will automatically trust new keys announced by a trusted server and remove any keys the server has removed, as long as they were added automatically
- The SSH Client now supports high resolutions and will display crisp text on high-DPI displays such as retina or 4K. The SSH Client now comes with new, higher resolution icons
- SSH Client profiles downloaded from the internet will now be considered unsafe. If a profile is marked by a browser using which it was downloaded as originating from an unsafe zone, the SSH Client will now load safe parts only. When loading a profile interactively in the graphical SSH Client, a prompt will be displayed, allowing the user to mark the profile as safe. If the user confirms, the profile can be fully loaded
Cryptography:
- Bitvise SSH Server, SSH Client and FlowSsh once again support non-standard DSA keys larger than 1024 bits. We do not recommend using these keys, and new keys of this type cannot be generated. Also, these keys cannot be used when FIPS mode cryptography is enabled in Windows. Re-adding support for these keys is intended to resolve an obstacle that may still be preventing some users of 6.xx versions from upgrading
- When using Windows cryptography, Bitvise SSH Server, SSH Client and FlowSsh now implement a backup strategy for DH and ECDH key exchange. Windows implements key exchange, but it does not expose the agreed value in a form suitable for SSH. Bitvise software must retrieve the value by carefully traversing undocumented Windows structures. In versions 7.xx, this required our software to be upgraded to continue working after the Windows 10 1803 update. Our software will now log a warning and fall back to Crypto++ if it cannot perform key exchange because Windows internal structures have changed. However: if FIPS mode is enabled in Windows, this backup strategy is not used, and the software must be updated
- When importing keys, such as from files, the stage at which an import failed is now described in more detail
SSH session:
- Bitvise SSH Server and Client now support the elevation extension. In previous versions, if a Windows account with administrative rights connected to the SSH Server, the server would always elevate the session if possible. Otherwise, the user would not be able to get an elevated session because there was no way to convey the user's preference. With the elevation extension, the user can request a non-administrative security context by requesting no elevation (elevation is still applied by default). In command line clients including stermc, sexec and sftpc, this is controlled using the switch -elevation=n
- Bitvise SSH Server and Client now support the no-flow-control extension. This disables SSH flow control for clients that only support opening one channel. No flow control is now preferred by sftpc, stermc, sexec and spksc, which only need to open one channel in the SSH session. The graphical SSH Client does not support no-flow-control because it requires multiple channels
- Bitvise SSH Server and Client now support the ext-auth-info extension. This allows the server to respond to user authentication failures with more detailed information in situations where this is safe. For example, if the client attempts to perform a password change but the new password does not meet complexity requirements, the server can communicate this instead of making the user guess
- Bitvise SSH Server and Client now support the delay-compression extension. Delayed compression reduces attack surface for unauthenticated clients by delaying availability of compression until after a user is authenticated. The delay-compression extension is an improvement over previously supported alternatives: the zlib@openssh.com method contains a by-design race condition, while the approach of invoking a second key exchange doubles the overhead of establishing an SSH session
Terminal:
- Settings for the graphical xterm/vt100 terminal console window (totermw) are now stored in the SSH Client profile instead of in the Windows registry
SFTP:
- In the graphical SFTP interface, the Open and Edit commands will now be much more responsive if a transfer is already in progress. The in-progress transfer will be paused and the file associated with the Open or Edit command will be transferred as a priority
- Both the graphical SFTP interface and sftpc can now work with local paths longer than 259 characters, as well as unsafe paths not permitted by Windows in some contexts (e.g. "C:Com1file")
- A new file transfer mode, TextLf, is now supported. This works the same as AutoLf, but forces newline conversions without relying on file type detection
Tunneling:
- The SSH Client now displays the country (if available) of remote IP addresses. The SSH Client uses the MaxMind GeoLite2 Country database (under license). The country database comes with the SSH Client installation and is not automatically updated, other than by updating the SSH Client itself.
Command line clients:
- It is now easier to connect to SSH servers that accept connections on non-default ports. If no port is specified on the command line, but the SSH Client knows a host key for the destination server, the SSH Client will automatically connect to the port associated with the server in the host key database. If there are multiple port associations, however, the port still needs to be specified, unless one of them is 22.
- It is now easier to enable and disable individual algorithms with our command-line clients. Previously, to use non-default algorithms, either a -profile needed to be used, or a complete algorithm list had to be supplied using -hkey, -kex, -encr or -mac. It is now still possible to pass a whole list using the same parameters, or using their new aliases -hkeyAlgs, -kexAlgs, -encrAlgs or -macAlgs. In addition, it is possible to modify the default algorithm lists using -hkeyMod, -kexMod, -encrMod or -macMod. When using the "Mod" versions, provide a comma-separated list of algorithm names with optional prefixes. Names prefixed with "+" are added to the front of the list; names without a prefix are appended to the end; and names prefixed with "!" are removed. Example: -encrMod=+aes256-gcm,!3des-ctr
Utilities:
- The log utility now supports filesystem paths in Unicode
Bitvise SSH Client 7.46
- After the SSH session has been terminated by receiving EOF or sending SSH_MSG_DISCONNECT, FlowSsh will now discard any further outgoing SSH packets. This helps avoid a stall in processing and further improves the odds that all previously received data will be processed.
- File transfer: Fixed an issue where, if the connection was lost during a download while synchronization was being performed, the local file size would be reset to zero.
- stermc: Improved handling of default colors configured in -profile or using the -colors parameter when using non-bvterm terminals such as xterm or vt100. The screen is now cleared using the configured colors.
Bitvise SSH Client 7.45
- Bitvise SSH Server, SSH Client, and FlowSsh previously did not implement strict size limits or sanitization of content before displaying or logging strings received from a remote party. Much stricter size limits and sanitization are now implemented
- Bitvise SSH Server, SSH Client, and FlowSsh now report the size of the Diffie Hellman group actually used in DH key exchange. This is useful with key exchange methods that use DH group exchange, where there was previously no straightforward way to know what size group was used
- Importing an empty public key file would cause the SSH Client's Host key manager to hang indefinitely. Fixed.
- When loading an SSH Client profile, the SSH Client's Remote Desktop tab failed to update the Remote Desktop width and/or height if the new value was 0 (the default value). Fixed.
Bitvise SSH Client 7.44
- Cryptography: Implemented support for changes in Windows internal cryptographic structures in Windows Insider Preview Build 17704. This build was released to Windows Insiders in the Fast ring on June 27, 2018
- Users who need to use earlier versions of our software on new Windows builds that change internal structures can work around compatibility issues by using the following key exchange algorithms: Curve25519, ECDH over nistp256k1. These key exchange methods do not rely on Windows cryptography; however, our software does not provide them if FIPS mode is enabled in Windows. Other key exchange methods require upgrading our software to a version that supports the new Windows build
Bitvise SSH Client 7.43
File transfer:
- Fixed issues in past Bitvise software versions that resulted in incorrect file times when using subsecond times with SFTP protocol versions 4 and 6. This would result in incorrect last modified times after a file transfer which affected, on average, about one in several hundred files. Affected files would receive a last modified timestamp incorrect by up to 7+ minutes
Authentication:
- Fixed issues in password change dialog behavior if the original password was modified
Installation:
- Updated installer and uninstaller manifests to reduce the likelihood that Windows will incorrectly run the Program Compatibility Assistant during or after installation. This mainly affects older Windows versions such as Windows 7
Bitvise SSH Client 7.42
- The End User License Agreement has been updated to try to bring it closer to the requirements of states and their contractors. Terms are otherwise unchanged. Situations in which licenses can be transferred are now laid out so that no permission will be needed in most cases
- The SSH Client now includes a new build of the SSH Server Remote Control Panel (WRC) for use with SSH Server versions 7.21 and above. The new build incorporates improvements to the SSH Server Control Panel since version 7.26
- The SSH Client continues to include older versions of the Remote Control Panel for use with older SSH Server versions. Those remain unchanged
- The graphical SSH Client will no longer mark a profile as changed when a password is changed, but the password is not configured to be saved in the profile
Bitvise SSH Client 7.41
- This is not a new feature release, but a successor to 7.39 with continued maintenance updates. (We skip over versions containing zeros to avoid ambiguities. For example, 7.04 and 7.40 might both be referred to as "7.4")
- This version continues an upgrade amnesty. Any Bitvise SSH Client activation code that could activate a previous 7.xx version will also activate this version
SSH:
- Fixed an issue in zlib compression provided by the Crypto++ library. There existed a race condition which could cause data to be decompressed incorrectly in specific circumstances. (The circumstances required for this to happen do not appear to exist in the graphical Bitvise SSH Client or its command line clients)
- Fixed a denial of service attack vector. This remains to be described in more detail
File transfer:
- When performing unattended file transfers, the command line client sftpc would previously send a fire-and-forget SSH_FXP_CLOSE message followed by immediately closing the SFTP channel and the SSH session. Depending on circumstances such as network latency, Bitvise SSH Server versions up to and including 7.39 could fail to process the SSH_FXP_CLOSE request and incorrectly log that the final transfer may not have completed as intended. This has been fixed in the SSH Server with version 7.41. But also, sftpc will no longer send a fire-and-forget SSH_FXP_CLOSE before exiting
- In the SFTP interface of the graphical SSH Client, in the Move to... dialog, removed a limit that incorrectly prevented entering more than a fixed number of characters. This prevented use of the Move to feature with long paths and file names
Bitvise SSH Client 7.39
- SFTP: In past 7.xx versions, Bitvise SSH Client and FlowSsh would perform a Resume check regardless of the type of server if Overwrite was enabled for upload. We suspect this could cause creation of an empty file with the same name on servers that support creation of multiple files with the same name.
- The Resume check will no longer be performed when connected to a server that does not support SFTP v6 check-file and check-file-blocks extensions. With a server that supports these extensions, the Resume check will continue to be performed for Overwrite, since in this case Resume and Overwrite are the same operation.
Bitvise SSH Client 7.36
Development, licensing, and US export control:
- This is the first version of Bitvise SSH Server, SSH Client, and FlowSsh published from the United States.
- All assets, operations, relationships, and agreements related to Bitvise software development and licensing; including license agreements for use of Bitvise software by users; have been transferred from Bitvise Limited incorporated in Gibraltar, to Bitvise Limited now incorporated in Texas.
- Final builds are now performed in Texas. Our software development continues in Slovenia, Germany, and Hungary, and may include developers elsewhere in the future.
- This move is an administrative change. Our development, ownership, pricing, support, terms and policies and relationship to customers generally remain the same.
- For the purpose of export from the United States, our SSH Server, SSH Client and FlowSsh are self-classified as Mass-Market products using the ECCN 5D992, with the encryption authorization type identifier MMKT. These denote eligibility under License Exception ENC § 740.17(b)(1) of the Export Administration Regulations (EAR).
- Bitvise SSH Server, SSH Client, and FlowSsh now come with new license agreements. Users must review the new EULAs, even though the terms remain substantially the same. We apologize for this inconvenience, and have attempted to draft the agreements in a way that this might not be necessary very often.
SSH:
- Windows 10 version 1709, OS build 17046.1000, changed internal Windows structures in a way that prevented Bitvise SSH Server, SSH Client, and FlowSsh from obtaining the agreed value in DH or ECDH key exchange. This prevented successful SSH connections using this new Windows build. Fixed.
- There exist SSH implementations based on WeOnlyDo, e.g. freeSSHd, which might not send failure description and language tag fields when sending an SSH_MSG_CHANNEL_OPEN_FAILURE message. Bitvise SSH Server, SSH Client and FlowSsh will now behave as though these fields were sent as empty strings, instead of disconnecting due to an unexpected packet format.
sexec:
- Now supports the command line parameter -git, which is shorthand for the new parameters -cmdQuoted and -exitZero. This allows sexec to be more easily configured for use with Git.
- Now supports the command line parameter -cmdQuoted. This can be used when the remote command to execute is provided outside of the -cmd=... parameter, but is enclosed in single or double quotes.
- Now supports the command line parameter -exitZero. If the remote command executes and returns exit code 0, this will cause sexec to return exit code 0 as well.
- Now supports the command line parameter -p . This can be used to specify the port number instead of -port=.
- Fixed an issue which would cause sexec to interpret as its own parameter a port number passed as part of the remote command to be executed. This could cause sexec to fail, or to connect to the SSH server on an unintended port.
Bitvise SSH Client 7.35
SFTP GUI:
- Fixed an issue which would cause a crash when all files are removed from the download or upload queue.
- Fixed visual artifacts that would arise while resizing in the SFTP Download or Upload window.
SFTP compatibility:
- We have identified two compatibility issues in current and past versions of mod_sftp for ProFTPD:
- When using SFTP versions 4-6, when a client requests attributes not supported by mod_sftp, the server returns an incorrectly encoded response. With past Bitvise SSH Client and FlowSsh versions, this would result in a disconnect.
- When using SFTP version 6, mod_sftp indicates support for the check-file extensions, but disconnects if the client requests the server to hash a larger file block by block. This prevents Bitvise SSH Client and FlowSsh from performing hash-based synchronization of file content, which would normally be used instead of Resume or Overwrite if check-file extensions can be used.
- We expect these issues to be resolved in future mod_sftp versions. However, mod_sftp now comes configured by default to not send its version in the SSH version string. A client therefore cannot distinguish between a newer version that will contain these fixes, and an older version which does not.
- At this time, Bitvise SSH Client and FlowSsh will avoid the known compatibility issues by restricting SFTP protocol version to 3 when mod_sftp is detected. We would like to lift this restriction in the future if there arises a way to detect the mod_sftp version early enough.
We have identifed a compatibility issue with Van Dyke VShell:
- When using SFTP version 6, the VShell server indicates support for the check-file extensions, but does not support block-by-block hashing. This prevents Bitvise SSH Client and FlowSsh from performing hash-based synchronization of file content, which would normally be used instead of Resume or Overwrite if check-file extensions can be used.
- At this time, hash-based synchronization will be avoided when connecting to VShell, and Resume and Overwrite will be used instead.
- If VShell chooses to implement support for block-by-block hashing, Bitvise SSH Client and FlowSsh will once more use this functionality if the server advertises the extension name check-file-blocks in its su
 OperaOpera 117.0 Build 5408.39 (64-bit)
OperaOpera 117.0 Build 5408.39 (64-bit) PC RepairPC Repair Tool 2025
PC RepairPC Repair Tool 2025 PhotoshopAdobe Photoshop CC 2025 26.3 (64-bit)
PhotoshopAdobe Photoshop CC 2025 26.3 (64-bit) OKXOKX - Buy Bitcoin or Ethereum
OKXOKX - Buy Bitcoin or Ethereum iTop VPNiTop VPN 6.3.0 - Fast, Safe & Secure
iTop VPNiTop VPN 6.3.0 - Fast, Safe & Secure Premiere ProAdobe Premiere Pro CC 2025 25.1
Premiere ProAdobe Premiere Pro CC 2025 25.1 BlueStacksBlueStacks 10.41.661.1001
BlueStacksBlueStacks 10.41.661.1001 Hero WarsHero Wars - Online Action Game
Hero WarsHero Wars - Online Action Game TradingViewTradingView - Trusted by 60 Million Traders
TradingViewTradingView - Trusted by 60 Million Traders LockWiperiMyFone LockWiper (Android) 5.7.2
LockWiperiMyFone LockWiper (Android) 5.7.2








Comments and User Reviews